Tech + AI + Science NewsTech + AI + Science News
12 item(s)
Tech + AI + Science News
How finance teams use Codex
OpenAI News
How finance teams use Codex new
OpenAI News · 2026-05-12
See how finance teams can use Codex to build MBRs, reporting packs, variance bridges, model checks, and planning scenarios from real work inputs.
Tech + AI + Science News
How to make your text look futuristic
Hacker News
How to make your text look futuristic (2016) new
Hacker News · 2026-05-12
Comments

Tech + AI + Science News
Beyond Semantic Similarity
Hacker News
Beyond Semantic Similarity new
Hacker News · 2026-05-12
Comments

Tech + AI + Science News
The Rise of the Bullshittery
Hacker News
The Rise of the Bullshittery new
Hacker News · 2026-05-12
Comments
Tech + AI + Science News
CERT is releasing six CVEs for serious
Hacker News
CERT is releasing six CVEs for serious security vulnerabilities in dnsmasq new
Hacker News · 2026-05-12
Comments

Tech + AI + Science News
What Parameter Golf taught us about AI-assisted
OpenAI News
What Parameter Golf taught us about AI-assisted research new
OpenAI News · 2026-05-12
Parameter Golf brought together 1,000+ participants and 2,000+ submissions to explore AI-assisted machine learning research, coding agents, quantization, and novel model design under strict constraints.

Tech + AI + Science News
How NVIDIA engineers and researchers build with
OpenAI News
How NVIDIA engineers and researchers build with Codex new
OpenAI News · 2026-05-12
Teams use Codex with GPT-5.5 to ship production systems and turn research ideas into runnable experiments.
Tech + AI + Science News
AutoScout24 scales engineering with AI-powered workflows
OpenAI News
AutoScout24 scales engineering with AI-powered workflows new
OpenAI News · 2026-05-12
Learn how AutoScout24 Group uses Codex and ChatGPT to speed development cycles, improve code quality, and expand AI adoption.
Tech + AI + Science News
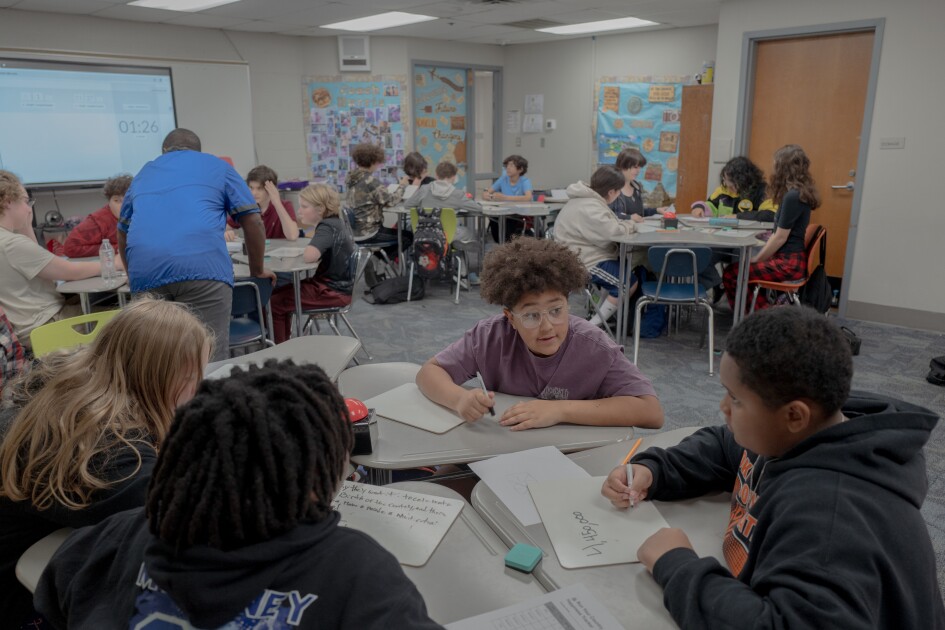
The Ed-Tech Backlash Is Here. What It
Brave News
The Ed-Tech Backlash Is Here. What It Means for Schools
Brave News
Most educators—74%—say their ... technology due to pushback or complaints from parents, according to the EdWeek Research Center survey. The percentage of districts dialing back tech use in school could rise as generative AI increasingly becomes integral to ed-tech tools, and educators, parents, and students see the downsides of too much AI use. Surveys from multiple organizations so far show that while parents want their children to learn how to use ...

Tech + AI + Science News
x2y Devs Tools: Innovating Developer Security and
Brave News
x2y Devs Tools: Innovating Developer Security and Productivity
Brave News
Introduction In the fast paced world of software development security and efficiency are paramount x2y Devs Tools a rising star in the developer tools industry has positioned itself as a trusted partner for developers and organizations seeking cutting edge solutions ...
Tech + AI + Science News
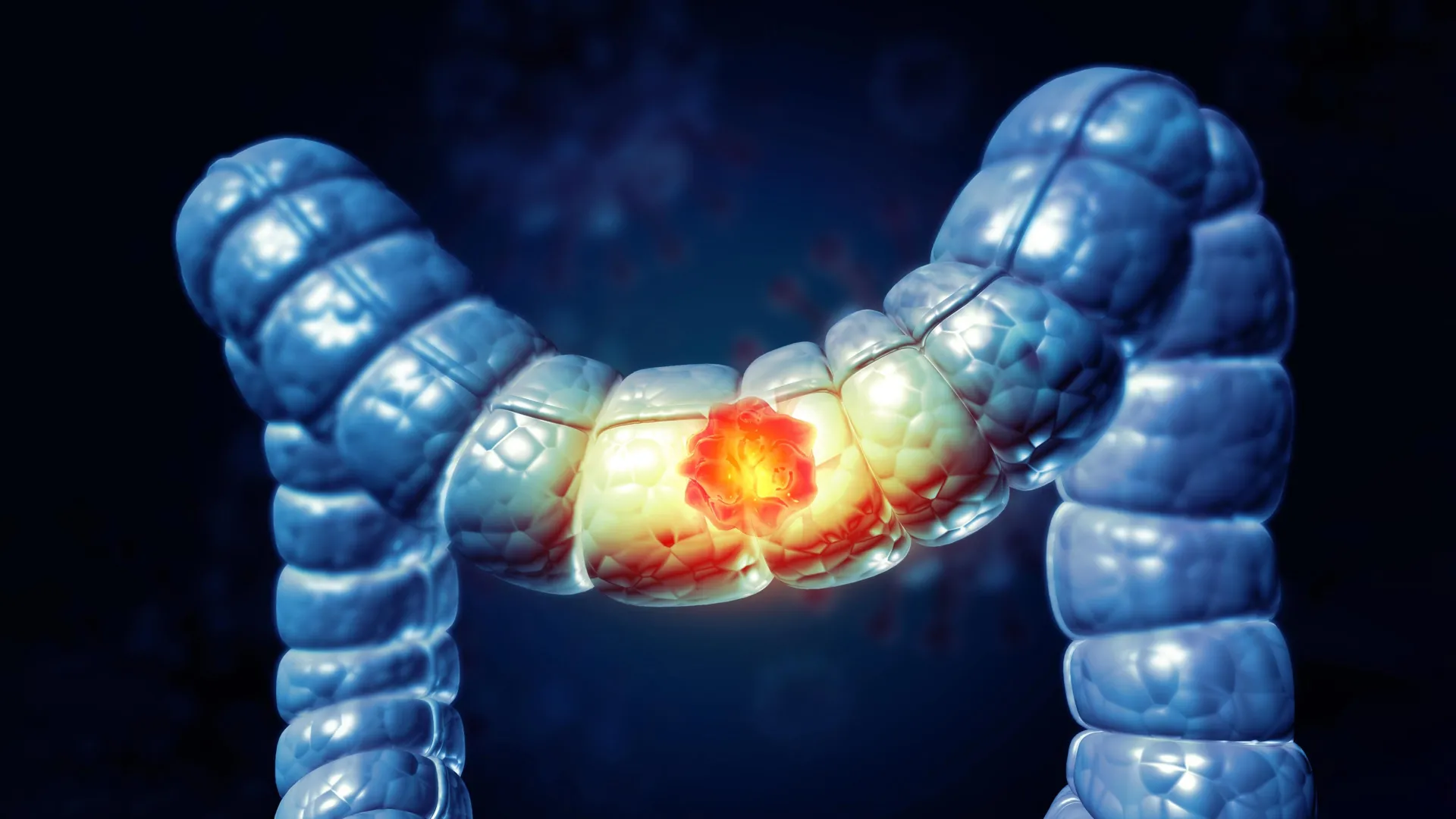
Colon cancer breakthrough keeps patients cancer-free for
Brave News
Colon cancer breakthrough keeps patients cancer-free for nearly 3 years | ScienceDaily new
Brave News
A short burst of immunotherapy before surgery is delivering surprisingly powerful results for a specific type of colorectal cancer. Patients in a UK-led trial who received just nine weeks of pembrolizumab prior to surgery have remained cancer-free nearly three years later—an outcome that ...

Tech + AI + Science News
SAP Patches Critical S/4HANA, Commerce Vulnerabilities -
Brave News
SAP Patches Critical S/4HANA, Commerce Vulnerabilities - SecurityWeek new
Brave News
SAP has released 15 new security notes, including two addressing critical code injection flaws in S/4HANA and Commerce.
Research (arXiv)
10 item(s)

Research (arXiv)
HarmoWAM: Harmonizing Generalizable and Precise Manipulation via
arXiv
HarmoWAM: Harmonizing Generalizable and Precise Manipulation via Adaptive World Action Models new
arXiv · 2026-05-11
World Action Models (WAMs) have emerged as a promising paradigm for robot control by modeling physical dynamics. Current WAMs generally follow two paradigms: the "Imagine-then-Execute" approach, which uses video prediction to infer actions via inverse dynamics, and the "Joint Modeling" approach, which jointly models actions and video representations. Based on systematic experiments, we observe a fundamental trade-off between these paradigms: the former explicitly leverages world models for generalizable transit but lacks interaction precision, whereas the latter enables fine-grained, temporally coherent action generation but is constrained by the exploration space of the training distribution. Motivated by these findings, we propose HarmoWAM, an end-to-end WAM that fully leverages a world model to unify predictive and reactive control, enabling both generalizable transit and precise mani

Research (arXiv)
A passive self-correcting quantum memory in three
arXiv
A passive self-correcting quantum memory in three dimensions new
arXiv · 2026-05-11
We construct a 3D Pauli stabilizer Hamiltonian whose ground state space can encode a qubit for exponential time when coupled to a bath at non-zero temperature. Our construction recursively applies a sequence of transformations to a seed Hamiltonian that increases the memory lifetime of the encoded qubit while maintaining geometric locality in $\mathbb{R}^3$.

Research (arXiv)
ELF: Embedded Language Flows
arXiv
ELF: Embedded Language Flows new
arXiv · 2026-05-11
Diffusion and flow-based models have become the de facto approaches for generating continuous data, e.g., in domains such as images and videos. Their success has attracted growing interest in applying them to language modeling. Unlike their image-domain counterparts, today's leading diffusion language models (DLMs) primarily operate over discrete tokens. In this paper, we show that continuous DLMs can be made effective with minimal adaptation to the discrete domain. We propose Embedded Language Flows (ELF), a class of diffusion models in continuous embedding space based on continuous-time Flow Matching. Unlike existing DLMs, ELF predominantly stays within the continuous embedding space until the final time step, where it maps to discrete tokens using a shared-weight network. This formulation makes it straightforward to adapt established techniques from image-domain diffusion models, e.g.

Research (arXiv)
Power Reinforcement Post-Training of Text-to-Image Models with
arXiv
Power Reinforcement Post-Training of Text-to-Image Models with Super-Linear Advantage Shaping new
arXiv · 2026-05-11
Recently, post-training methods based on reinforcement learning, with a particular focus on Group Relative Policy Optimization (GRPO), have emerged as the robust paradigm for further advancement of text-to-image (T2I) models. However, these methods are often prone to reward hacking, wherein models exploit biases in imperfect reward functions rather than yielding genuine performance gains. In this work, we identify that normalization could lead to miscalibration and directly removing the prompt-level standard deviation term yields an optimal policy ascent direction that is linear in the advantage but still limits the separation of genuine signals from noise. To mitigate the above issues, we propose Super-Linear Advantage Shaping (SLAS) by revisiting the functional update from an information geometry perspective. By extending the Fisher-Rao information metric with advantage-dependent weigh

Research (arXiv)
Personal Visual Context Learning in Large Multimodal
arXiv
Personal Visual Context Learning in Large Multimodal Models new
arXiv · 2026-05-11
As wearable devices like smart glasses integrate Large Multimodal Models (LMMs) into the continuous first-person visual streams of individual users, the evolution of these models into true personal assistants hinges on visual personalization: the ability to reason over visual information unique to the wearer. We formalize this capability as Personal Visual Context Learning (Personal VCL), the prompt-time capability of using user-specific visual context to resolve personalized queries. To systematically evaluate this, we present Personal-VCL-Bench, a comprehensive benchmark capturing the personal visual world across persons, objects, and behaviors. Our analysis of frontier LMMs identifies a profound context utilization gap, revealing that the mechanisms for leveraging visual evidence, as well as aggregating multiple visual observations, remain critically understudied. Motivated by these f

Research (arXiv)
Variational Inference for Lévy Process-Driven SDEs via
arXiv
Variational Inference for Lévy Process-Driven SDEs via Neural Tilting new
arXiv · 2026-05-11
Modelling extreme events and heavy-tailed phenomena is central to building reliable predictive systems in domains such as finance, climate science, and safety-critical AI. While Lévy processes provide a natural mathematical framework for capturing jumps and heavy tails, Bayesian inference for Lévy-driven stochastic differential equations (SDEs) remains intractable with existing methods: Monte Carlo approaches are rigorous but lack scalability, whereas neural variational inference methods are efficient but rely on Gaussian assumptions that fail to capture discontinuities. We address this tension by introducing a neural exponential tilting framework for variational inference in Lévy-driven SDEs. Our approach constructs a flexible variational family by exponentially reweighting the Lévy measure using neural networks. This parametrization preserves the jump structure of the underlying proces

Research (arXiv)
DECO: Sparse Mixture-of-Experts with Dense-Comparable Performan…
arXiv
DECO: Sparse Mixture-of-Experts with Dense-Comparable Performance on End-Side Devices new
arXiv · 2026-05-11
While Mixture-of-Experts (MoE) scales model capacity without proportionally increasing computation, its massive total parameter footprint creates significant storage and memory-access bottlenecks, which hinder efficient end-side deployment that simultaneously requires high performance, low computational cost, and small storage overhead. To achieve these properties, we present DECO, a sparse MoE architecture designed to match the performance of dense Transformers under identical total parameter budgets and training tokens. DECO utilizes the differentiable and flexible ReLU-based routing enhanced by learnable expert-wise scaling, which adaptively balances the contributions of routed and shared experts. Furthermore, we introduce NormSiLU, an activation function that normalizes inputs prior to SiLU operators, producing a more stable trend of routed-expert activation ratio and a higher intrin

Research (arXiv)
Crystallographic Symmetry Generates Phononic Holonomic Gates wi…
arXiv
Crystallographic Symmetry Generates Phononic Holonomic Gates with Biased-Erasure Channels new
arXiv · 2026-05-11
Solid-state processors require control layers whose errors are legible to quantum-error-correction decoders. We show that crystallographic symmetry can provide such a layer in strain-active Lambda manifolds. When the projected strain tensor and Lambda-transition operators share a multiplicity-one two-dimensional irreducible representation, symmetry fixes the linear strain interaction to a scalar dot product. Two phase-locked mechanical modes synthesize a circular strain field, enabling complex phononic Lambda-leg control without local microwave near fields. On this manifold we construct a superadiabatic echo-lune holonomic gate using Lambda-leg control and a resonant double-quantum counterdiabatic tone. Rotating-frame simulations of a nitrogen-vacancy center give 99.88% conditional average fidelity in 1.833 microseconds, or 99.40% when leakage is counted as error. A resonant gigahertz hi

Research (arXiv)
Quantifying Concentration Phenomena of Mean-Field Transformers…
arXiv
Quantifying Concentration Phenomena of Mean-Field Transformers in the Low-Temperature Regime new
arXiv · 2026-05-11
Transformers with self-attention modules as their core components have become an integral architecture in modern large language and foundation models. In this paper, we study the evolution of tokens in deep encoder-only transformers at inference time which is described in the large-token limit by a mean-field continuity equation. Leveraging ideas from the convergence analysis of interacting multi-particle systems, with particles corresponding to tokens, we prove that the token distribution rapidly concentrates onto the push-forward of the initial distribution under a projection map induced by the key, query, and value matrices, and remains metastable for moderate times. Specifically, we show that the Wasserstein distance of the two distributions scales like $\sqrt{{\log(β+1)}/β}\exp(Ct)+\exp(-ct)$ in terms of the temperature parameter $β^{-1}\to 0$ and inference time $t\geq 0$. For the p

Research (arXiv)
Efficient Admissible Set Projection in Optimization-based Invar…
arXiv
Efficient Admissible Set Projection in Optimization-based Invariant-Domain-Preserving Limiters for Ideal MHD new
arXiv · 2026-05-11
Preserving the admissible set of the ideal magnetohydrodynamics (MHD) equations is important not only for producing physically meaningful numerical solutions, but more importantly for achieving robust computations. In this paper, we develop an optimization-based limiter to enforce admissibility while preserving global conservation and accuracy. For an easy and efficient projection, we decompose the admissible set into slices parameterized by the magnetic energy, so that the MHD projection reduces to a one-dimensional minimization, which can be solved efficiently by the Brent method. The splitting method can be used to efficiently solve the global minimization problem of the optimization-based limiter, which can be used to enforce cell average admissibility in discontinuous Galerkin (DG) schemes, and pointwise admissibility can be further enforced by the Zhang-Shu positivity-preserving li
Security (NVD + CISA KEV)
14 item(s)

Security (NVD + CISA KEV)
CVE-2014-2206· CVSS 10.0 HIGH
NVD
CVE-2014-2206· CVSS 10.0 HIGH
NVD · 2014-03-05
Stack-based buffer overflow in GetGo Download Manager 4.9.0.1982, 4.8.2.1346, 4.4.5.502, and earlier allows remote attackers to cause a denial of service (crash) and execute arbitrary code via a long HTTP Response Header.

Security (NVD + CISA KEV)
CVE-2014-0683· CVSS 10.0 HIGH
NVD
CVE-2014-0683· CVSS 10.0 HIGH
NVD · 2014-03-06
The web management interface on the Cisco RV110W firewall with firmware 1.2.0.9 and earlier, RV215W router with firmware 1.1.0.5 and earlier, and CVR100W router with firmware 1.0.1.19 and earlier does not prevent replaying of modified authentication requests, which allows remote attackers to obtain administrative access by leveraging the ability to intercept requests, aka Bug IDs CSCul94527, CSCum86264, and CSCum86275.

Security (NVD + CISA KEV)
CVE-2014-0703· CVSS 10.0 HIGH
NVD
CVE-2014-0703· CVSS 10.0 HIGH
NVD · 2014-03-06
Cisco Wireless LAN Controller (WLC) devices 7.4 before 7.4.110.0 distribute Aironet IOS software with a race condition in the status of the administrative HTTP server, which allows remote attackers to bypass intended access restrictions by connecting to an Aironet access point on which this server had been disabled ineffectively, aka Bug ID CSCuf66202.

Security (NVD + CISA KEV)
CVE-2013-6941· CVSS 10.0 HIGH
NVD
CVE-2013-6941· CVSS 10.0 HIGH
NVD · 2014-03-11
Unspecified vulnerability in Citrix NetScaler Application Delivery Controller (ADC) 9.3.x before 9.3-64.4, 10.0 before 10.0-77.5, and 10.1 before 10.1-118.7 allows users to "breakout" of the shell via unknown vectors.

Security (NVD + CISA KEV)
CVE-2014-2321· CVSS 10.0 HIGH
NVD
CVE-2014-2321· CVSS 10.0 HIGH
NVD · 2014-03-11
web_shell_cmd.gch on ZTE F460 and F660 cable modems allows remote attackers to obtain administrative access via sendcmd requests, as demonstrated by using "set TelnetCfg" commands to enable a TELNET service with specified credentials.

Security (NVD + CISA KEV)
CVE-2014-0505· CVSS 10.0 HIGH
NVD
CVE-2014-0505· CVSS 10.0 HIGH
NVD · 2014-03-14
Adobe Shockwave Player before 12.1.0.150 allows remote attackers to execute arbitrary code or cause a denial of service (memory corruption) via unspecified vectors.

Security (NVD + CISA KEV)
CVE-2014-1704· CVSS 10.0 HIGH
NVD
CVE-2014-1704· CVSS 10.0 HIGH
NVD · 2014-03-16
Multiple unspecified vulnerabilities in Google V8 before 3.23.17.18, as used in Google Chrome before 33.0.1750.149, allow attackers to cause a denial of service or possibly have other impact via unknown vectors.

Security (NVD + CISA KEV)
CVE-2014-1708· CVSS 10.0 HIGH
NVD
CVE-2014-1708· CVSS 10.0 HIGH
NVD · 2014-03-16
The boot implementation in Google Chrome OS before 33.0.1750.152 does not properly consider file persistence, which allows remote attackers to execute arbitrary code via unspecified vectors.

Security (NVD + CISA KEV)
CVE-2014-1512· CVSS 10.0 HIGH
NVD
CVE-2014-1512· CVSS 10.0 HIGH
NVD · 2014-03-19
Use-after-free vulnerability in the TypeObject class in the JavaScript engine in Mozilla Firefox before 28.0, Firefox ESR 24.x before 24.4, Thunderbird before 24.4, and SeaMonkey before 2.25 allows remote attackers to execute arbitrary code by triggering extensive memory consumption while garbage collection is occurring, as demonstrated by improper handling of BumpChunk objects.

Security (NVD + CISA KEV)
CVE-2014-2523· CVSS 10.0 HIGH
NVD
CVE-2014-2523· CVSS 10.0 HIGH
NVD · 2014-03-24
net/netfilter/nf_conntrack_proto_dccp.c in the Linux kernel through 3.13.6 uses a DCCP header pointer incorrectly, which allows remote attackers to cause a denial of service (system crash) or possibly execute arbitrary code via a DCCP packet that triggers a call to the (1) dccp_new, (2) dccp_packet, or (3) dccp_error function.

Security (NVD + CISA KEV)
CVE-2012-4886· CVSS 10.0 HIGH
NVD
CVE-2012-4886· CVSS 10.0 HIGH
NVD · 2014-03-24
Stack-based buffer overflow in wpsio.dll in Kingsoft WPS Office 2012 possibly 8.1.0.3238 allows remote attackers to execute arbitrary code via a long BSTR string.

Security (NVD + CISA KEV)
CVE-2014-1300· CVSS 10.0 HIGH
NVD
CVE-2014-1300· CVSS 10.0 HIGH
NVD · 2014-03-26
Unspecified vulnerability in Apple Safari 7.0.2 on OS X allows remote attackers to execute arbitrary code with root privileges via unknown vectors, as demonstrated by Google during a Pwn4Fun competition at CanSecWest 2014.

Security (NVD + CISA KEV)
CVE-2014-1303· CVSS 10.0 HIGH
NVD
CVE-2014-1303· CVSS 10.0 HIGH
NVD · 2014-03-26
Heap-based buffer overflow in Apple Safari 7.0.2 allows remote attackers to execute arbitrary code and bypass a sandbox protection mechanism via unspecified vectors, as demonstrated by Liang Chen during a Pwn2Own competition at CanSecWest 2014.

Security (NVD + CISA KEV)
CVE-2014-0506· CVSS 10.0 HIGH
NVD
CVE-2014-0506· CVSS 10.0 HIGH
NVD · 2014-03-27
Use-after-free vulnerability in Adobe Flash Player before 11.7.700.275 and 11.8.x through 13.0.x before 13.0.0.182 on Windows and OS X and before 11.2.202.350 on Linux, Adobe AIR before 13.0.0.83 on Android, Adobe AIR SDK before 13.0.0.83, and Adobe AIR SDK & Compiler before 13.0.0.83 allows remote attackers to execute arbitrary code, and possibly bypass an Internet Explorer sandbox protection mechanism, via unspecified vectors, as demonstrated by VUPEN during a Pwn2Own competition at CanSecWest 2014.
Projects + Resources (Discovery)
10 item(s)

Projects + Resources (Discovery)
Apprenez à programmer avec JavaScript - OpenClassrooms
Brave Search
Apprenez à programmer avec JavaScript - OpenClassrooms new
Brave Search
Maîtrisez les bases de la programmation JavaScript et sa logique de programmation en réalisant un site web dynamique. ... Les applications s'appuient sur des données et une logique pour accomplir leur magie. Cela exige qu'un programmeur – vous – indique à l'ordinateur ce qu'il faut faire et comment. Alors, comment écrire une application ? Par où commencer ? Dans ce cours, vous découvrirez les bases du langage de programmation JavaScript : sa syntaxe, sa logique de programmation…

Projects + Resources (Discovery)
Le Tutoriel JavaScript Moderne
Brave Search
Le Tutoriel JavaScript Moderne new
Brave Search
Tutoriel JavaScript moderne : explications simples mais détaillées avec des exemples et des exercices, y compris : les closures, le document et les événements, la programmation orientée objet et plus encore.
Projects + Resources (Discovery)
Apprendre JavaScript | Grafikart
Brave Search
Apprendre JavaScript | Grafikart new
Brave Search
Dans cette série de vidéos vous découvrirez les erreurs classiques qui peuvent se produire en JavaScript ainsi que les outils qui...

Projects + Resources (Discovery)
Machine Learning Mastering Course in Arabic |
Brave Search
Machine Learning Mastering Course in Arabic | Udemy new
Brave Search
DevelopmentData ScienceMachine Learning · Preview this course · الكورس الاحترافي في الذكاء الاصطناعي · Rating: 4.4 out of 54.4 (204 ratings) 14,496 students · Created by Ahmed Elesawy · Last updated 8/2024 · Arabic · Arabic [Auto] Preview this course ·

Projects + Resources (Discovery)
Online Course: Machine Learning Mastering Course in
Brave Search
Online Course: Machine Learning Mastering Course in Arabic from Udemy | Class Central new
Brave Search
Start your review of Machine Learning Mastering Course in Arabic · Facebook · Twitter · Bluesky · Email · Copy link · Get personalized course recommendations, track subjects and courses with reminders, and more. Sign up for free

Projects + Resources (Discovery)
Free Online Course -Machine learning and Deep
Brave Search
Free Online Course -Machine learning and Deep learning from scratch in Arabic | Coursesity new
Brave Search
To Learn machine learning , <strong>Be a learning Machine</strong> - Free Course

Projects + Resources (Discovery)
Learn Python in Arabic #001 - Introduction
Brave Search
Learn Python in Arabic #001 - Introduction And What's Python - YouTube new
Brave Search
Paid Courses<strong>https://www.elzero.courses/</strong>Get Your Personal Websitehttps://www.youtube.com/watch?v=4ydvMB3Vtc0Academy Websitehttps://www.elzero.orgIntroduction ...

Projects + Resources (Discovery)
Python For Beginners In Arabic تعلم لغة
Brave Search
Python For Beginners In Arabic تعلم لغة البايثون new
Brave Search
Welcome to the <strong>Python For Beginners In Arabic</strong> In this course we cover python language structured programming concepts and Object oriented concepts · we will Learn Programming Concepts using Python3 Language.
Projects + Resources (Discovery)
Free Video: Learn JavaScript in Arabic from
Brave Search
Free Video: Learn JavaScript in Arabic from YouTube | Class Central new
Brave Search
<strong>Learn JavaScript In Arabic 2021</strong> - #002 - How To Study The Course ?. <strong>Learn JavaScript In Arabic 2021</strong> - #003 - Setting Up Environment And Tools. <strong>Learn JavaScript In Arabic 2021</strong> - #004 - Work With Chrome Developer Tools.

Projects + Resources (Discovery)
Curso intensivo de machine learning
Brave Search
Curso intensivo de machine learning new
Brave Search
Google's fast-paced, practical introduction to machine learning, featuring a series of animated videos, interactive visualizations, and hands-on practice exercises.