Tech + AI + Science NewsTech + AI + Science News
14 item(s)
Tech + AI + Science News
OpenAI Campus Network: Student club interest form
OpenAI News
OpenAI Campus Network: Student club interest form new
OpenAI News · 2026-05-11
Join the OpenAI Campus Network—connect student clubs worldwide, access AI tools, host events, and build an AI-powered campus community.

Tech + AI + Science News
How enterprises are scaling AI
OpenAI News
How enterprises are scaling AI new
OpenAI News · 2026-05-11
How enterprises scale AI: from early experiments to compounding impact through trust, governance, workflow design, and quality at scale.
Tech + AI + Science News
TanStack NPM Packages Compromised
Hacker News
TanStack NPM Packages Compromised new
Hacker News · 2026-05-11
Comments

Tech + AI + Science News
I let AI build a tool to
Hacker News
I let AI build a tool to help me figure out what was waking me up at night new
Hacker News · 2026-05-11
Comments
Tech + AI + Science News
GitLab Announces Workforce Reduction and End of
Hacker News
GitLab Announces Workforce Reduction and End of Their CREDIT Values new
Hacker News · 2026-05-11
Comments
Tech + AI + Science News
Library for fast mapping of Java records
Hacker News
Library for fast mapping of Java records to native memory new
Hacker News · 2026-05-11
Comments

Tech + AI + Science News
Running Codex safely at OpenAI
OpenAI News
Running Codex safely at OpenAI
OpenAI News · 2026-05-08
How OpenAI runs Codex securely with sandboxing, approvals, network policies, and agent-native telemetry to support safe and compliant coding agent adoption.

Tech + AI + Science News
The AWS outage post-mortem is more revealing
Brave News
The AWS outage post-mortem is more revealing in what it doesn’t say new
Brave News
The company listed all of the systems that went haywire, but never really identified what happened differently that day to cause problems. Worse yet, putting out technology brushfires this way leaves the forest in danger of burning again.

Tech + AI + Science News
LLM Leaderboard 2026: Best AI Models Benchmark
Brave News
LLM Leaderboard 2026: Best AI Models Benchmark & Ranking
Brave News
The definitive LLM leaderboard. See which AI model leads on reasoning, coding, speed & cost from $0.02 to $25/M tokens across 356+ models.
Tech + AI + Science News
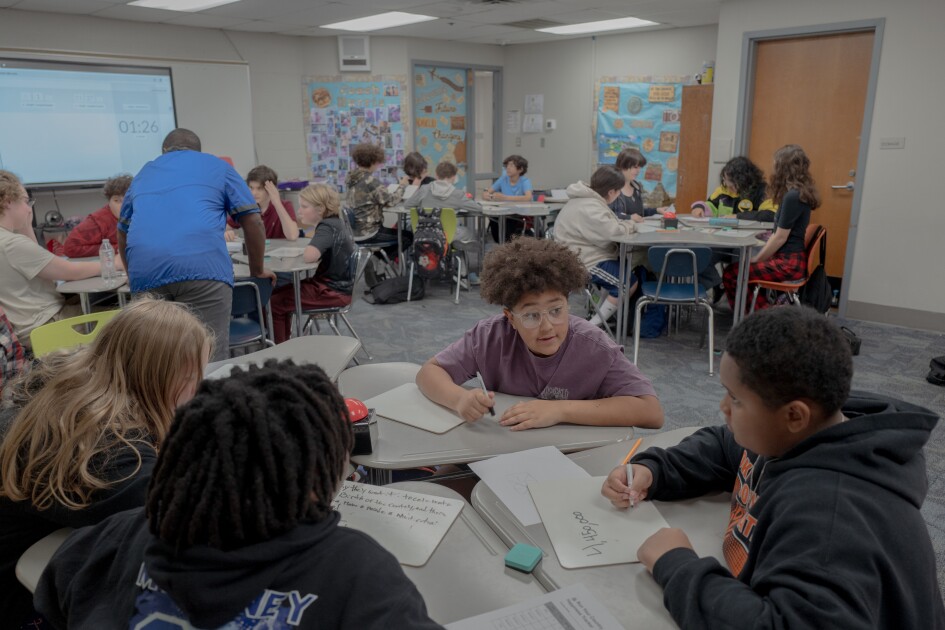
The Ed-Tech Backlash Is Here. What It
Brave News
The Ed-Tech Backlash Is Here. What It Means for Schools new
Brave News
Most educators—74%—say their ... technology due to pushback or complaints from parents, according to the EdWeek Research Center survey. The percentage of districts dialing back tech use in school could rise as generative AI increasingly becomes integral to ed-tech tools, and educators, parents, and students see the downsides of too much AI use. Surveys from multiple organizations so far show that while parents want their children to learn how to use ...

Tech + AI + Science News
x2y Devs Tools: Innovating Developer Security and
Brave News
x2y Devs Tools: Innovating Developer Security and Productivity new
Brave News
Introduction In the fast paced world of software development security and efficiency are paramount x2y Devs Tools a rising star in the developer tools industry has positioned itself as a trusted partner for developers and organizations seeking cutting edge solutions ...
Tech + AI + Science News
GitHub for Beginners: Getting started with OSS
GitHub Blog
GitHub for Beginners: Getting started with OSS contributions new
GitHub Blog · 2026-05-11
Learn how to find opportunities to contribute to the open source community. The post GitHub for Beginners: Getting started with OSS contributions appeared first on The GitHub Blog .

Tech + AI + Science News
Why age assurance laws matter for developers
GitHub Blog
Why age assurance laws matter for developers
GitHub Blog · 2026-05-08
Youth safety requirements are moving down the tech stack to operating systems and app stores—raising new questions for open source developers. The post Why age assurance laws matter for developers appeared first on The GitHub Blog .
Tech + AI + Science News
How researchers are using GitHub Innovation Graph
GitHub Blog
How researchers are using GitHub Innovation Graph data to reveal the “digital complexity” of nations
GitHub Blog · 2026-05-08
Researchers share in an interview how they used GitHub data to predict GDP, inequality, and emissions in ways that traditional economic data misses, along with our Q4 2025 data release. The post How researchers are using GitHub Innovation Graph data to reveal the “digital complexity” of nations appeared first on The GitHub Blog .
Research (arXiv)
10 item(s)
Research (arXiv)
123D: Unifying Multi-Modal Autonomous Driving Data at
arXiv
123D: Unifying Multi-Modal Autonomous Driving Data at Scale new
arXiv · 2026-05-08
The pursuit of autonomous driving has produced one of the richest sensor data collections in all of robotics. However, its scale and diversity remain largely untapped. Each dataset adopts different 2D and 3D modalities, such as cameras, lidar, ego states, annotations, traffic lights, and HD maps, with different rates and synchronization schemes. They come in fragmented formats requiring complex dependencies that cannot natively coexist in the same development environment. Further, major inconsistencies in annotation conventions prevent training or measuring generalization across multiple datasets. We present 123D, an open-source framework that unifies such multi-modal driving data through a single API. To handle synchronization, we store each modality as an independent timestamped event stream with no prescribed rate, enabling synchronous or asynchronous access across arbitrary datasets.
Research (arXiv)
LLMs Improving LLMs: Agentic Discovery for Test-Time
arXiv
LLMs Improving LLMs: Agentic Discovery for Test-Time Scaling new
arXiv · 2026-05-08
Test-time scaling (TTS) has become an effective approach for improving large language model performance by allocating additional computation during inference. However, existing TTS strategies are largely hand-crafted: researchers manually design reasoning patterns and tune heuristics by intuition, leaving much of the computation-allocation space unexplored. We propose an environment-driven framework, AutoTTS, that changes what researchers design: from individual TTS heuristics to environments where TTS strategies can be discovered automatically. The key to AutoTTS lies in environment construction: the discovery environment must make the control space tractable and provide cheap, frequent feedback for TTS search. As a concrete instantiation, we formulate width--depth TTS as controller synthesis over pre-collected reasoning trajectories and probe signals, where controllers decide when to b
Research (arXiv)
Advances in quantum learning theory with bosonic
arXiv
Advances in quantum learning theory with bosonic systems new
arXiv · 2026-05-08
This paper reviews recent advances in quantum learning theory for continuous-variable (CV) systems. Quantum learning theory investigates how to extract classical information from quantum systems as efficiently as possible. CV systems are ubiquitous in nature and in quantum technologies, as they describe bosonic and quantum-optical systems. While quantum learning theory for finite-dimensional systems has been extensively studied, the corresponding theory for CV systems has only recently begun to develop; here we provide a concise review. We focus on the following questions: what is the minimum number of copies (the sample complexity) required to learn a non-Gaussian state, possibly under energy constraints? What is the sample complexity for learning Gaussian states? How does the performance of CV state learning depend on non-Gaussianity? How can one test whether a state is Gaussian or far
Research (arXiv)
Normalizing Trajectory Models
arXiv
Normalizing Trajectory Models new
arXiv · 2026-05-08
Diffusion-based models decompose sampling into many small Gaussian denoising steps -- an assumption that breaks down when generation is compressed to a few coarse transitions. Existing few-step methods address this through distillation, consistency training, or adversarial objectives, but sacrifice the likelihood framework in the process. We introduce Normalizing Trajectory Models (NTM), which models each reverse step as an expressive conditional normalizing flow with exact likelihood training. Architecturally, NTM combines shallow invertible blocks within each step with a deep parallel predictor across the trajectory, forming an end-to-end network trainable from scratch or initializable from pretrained flow-matching models. Its exact trajectory likelihood further enables self-distillation: a lightweight denoiser trained on the model's own score produces high-quality samples in four step
Research (arXiv)
Conformal Path Reasoning: Trustworthy Knowledge Graph Question
arXiv
Conformal Path Reasoning: Trustworthy Knowledge Graph Question Answering via Path-Level Calibration new
arXiv · 2026-05-08
Knowledge Graph Question Answering (KGQA) has shown promise for grounded and interpretable reasoning, yet existing approaches often fail to provide reliable coverage guarantees over retrieved answers. While Conformal Prediction (CP) offers a principled framework for producing prediction sets with statistical guarantees, prior methods suffer from critical limitations in both calibration validity and score discriminability, resulting in violated coverage guarantees and excessively large prediction sets. To address these pitfalls, we propose Conformal Path Reasoning (CPR), a trustworthy KGQA framework with two key innovations. First, we perform query-level conformal calibration over path-level scores, preserving the exchangeability while generating path prediction sets. Second, we introduce the Residual Conformal Value Network (RCVNet), a lightweight module trained via PUCT-guided explorati
Research (arXiv)
Unlocking vacuum entanglement
arXiv
Unlocking vacuum entanglement new
arXiv · 2026-05-08
The structure of entanglement in the ground state of the harmonic chain is studied. A class of two-mode squeezed states, useful for this purpose, is identified. The entanglement of the local modes at the ends of the chain, after tracing out the centre, rapidly falls to zero as the length of the chain increases. However, if the central modes are measured, and the result communicated to systems interacting with the outer modes, the latter exhibit greatly enhanced entanglement, including in conditions where none was otherwise available. These ideas can be demonstrated in experiments in trapped ions, among other systems. The extension to the continuous case yields enhanced entanglement extracted from the vacuum state of a bosonic quantum field.
Research (arXiv)
Zero-Shot Imagined Speech Decoding via Imagined-to-Listened MEG
arXiv
Zero-Shot Imagined Speech Decoding via Imagined-to-Listened MEG Mapping new
arXiv · 2026-05-08
Decoding imagined speech from non-invasive brain recordings is challenging because imagined datasets are scarce and difficult to align temporally across subjects and sessions In this work, we propose a new approach to the decoding of imagined speech that leverages the richer and more reliably labeled recordings during listening to speech. We collected paired listened and imagined MEG recordings to rhythmic melodic and spoken stimuli from trained musicians. Using trained musicians helped improve temporal alignment across conditions. We then developed a three-stage decoding pipeline that revealed consistent and meaningful relationships between neural activity evoked by imagining and listening to the same stimuli. First, we trained six linear and neural models to map imagined MEG responses to listened responses. We evaluated these models against a null baseline from unseen subjects to valid
Research (arXiv)
GRAPHLCP: Structure-Aware Localized Conformal Prediction on Gra…
arXiv
GRAPHLCP: Structure-Aware Localized Conformal Prediction on Graphs new
arXiv · 2026-05-08
Conformal prediction (CP) provides a distribution-free approach to uncertainty quantification with finite-sample guarantees. However, applying CP to graph neural networks (GNNs) remains challenging as the combinatorial nature of graphs often leads to insufficiently certain predictions and indiscriminative embeddings. Existing methods primarily rely on embedding-space proximity for localization, which can be unreliable for graphs and yield inefficient prediction sets. We propose GRAPHLCP, a proximity-based localized CP framework that explicitly incorporates graph topology and inter-node dependencies into localization and weighting. Our approach introduces a feature-aware densification step to mitigate locality bias in sparse graphs, followed by a Personalized PageRank-based kernel computation to model structural proximity. This enables topology-dependent anchor sampling and calibration we
Research (arXiv)
EmambaIR: Efficient Visual State Space Model for
arXiv
EmambaIR: Efficient Visual State Space Model for Event-guided Image Reconstruction new
arXiv · 2026-05-08
Recent event-based image reconstruction methods predominantly rely on Convolutional Neural Networks (CNNs) and Vision Transformers (ViTs) to process complementary event information. However, these architectures face fundamental limitations: CNNs often fail to capture global feature correlations, whereas ViTs incur quadratic computational complexity (e.g., $O(n^2)$), hindering their application in high-resolution scenarios. To address these bottlenecks, we introduce EmambaIR, an Efficient visual State Space Model designed for image reconstruction using spatially sparse and temporally continuous event streams. Our framework introduces two key components: the cross-modal Top-k Sparse Attention Module (TSAM) and the Gated State-Space Module (GSSM). TSAM efficiently performs pixel-level top-k sparse attention to guide cross-modal interactions, yielding rich yet sparse fusion features. Subsequ
Research (arXiv)
A Note on Non-Negative $L_1$-Approximating Polynomials
arXiv
A Note on Non-Negative $L_1$-Approximating Polynomials new
arXiv · 2026-05-08
$L_1$-Approximating polynomials, i.e., polynomials that approximate indicator functions in $L_1$-norm under certain distributions, are widely used in computational learning theory. We study the existence of \textit{non-negative} $L_1$-approximating polynomials with respect to Gaussian distributions. This is a stronger requirement than $L_1$-approximation but weaker than sandwiching polynomials (which themselves have many applications). These non-negative approximating polynomials have recently found uses in smoothed learning from positive-only examples. In this short note, we prove that every class of sets with Gaussian surface area (GSA) at most $Γ$ under the standard Gaussian admits degree-$k$ non-negative polynomials that $\eps$-approximate its indicator functions in $L_1$-norm, for $k=\tilde{O}(Γ^2/\varepsilon^2)$. Equivalently, finite GSA implies $L_1$-approximation with the stronge
Security (NVD + CISA KEV)
14 item(s)
Security (NVD + CISA KEV)
CVE-2014-2206· CVSS 10.0 HIGH
NVD
CVE-2014-2206· CVSS 10.0 HIGH
NVD · 2014-03-05
Stack-based buffer overflow in GetGo Download Manager 4.9.0.1982, 4.8.2.1346, 4.4.5.502, and earlier allows remote attackers to cause a denial of service (crash) and execute arbitrary code via a long HTTP Response Header.
Security (NVD + CISA KEV)
CVE-2014-0683· CVSS 10.0 HIGH
NVD
CVE-2014-0683· CVSS 10.0 HIGH
NVD · 2014-03-06
The web management interface on the Cisco RV110W firewall with firmware 1.2.0.9 and earlier, RV215W router with firmware 1.1.0.5 and earlier, and CVR100W router with firmware 1.0.1.19 and earlier does not prevent replaying of modified authentication requests, which allows remote attackers to obtain administrative access by leveraging the ability to intercept requests, aka Bug IDs CSCul94527, CSCum86264, and CSCum86275.
Security (NVD + CISA KEV)
CVE-2014-0703· CVSS 10.0 HIGH
NVD
CVE-2014-0703· CVSS 10.0 HIGH
NVD · 2014-03-06
Cisco Wireless LAN Controller (WLC) devices 7.4 before 7.4.110.0 distribute Aironet IOS software with a race condition in the status of the administrative HTTP server, which allows remote attackers to bypass intended access restrictions by connecting to an Aironet access point on which this server had been disabled ineffectively, aka Bug ID CSCuf66202.
Security (NVD + CISA KEV)
CVE-2013-6941· CVSS 10.0 HIGH
NVD
CVE-2013-6941· CVSS 10.0 HIGH
NVD · 2014-03-11
Unspecified vulnerability in Citrix NetScaler Application Delivery Controller (ADC) 9.3.x before 9.3-64.4, 10.0 before 10.0-77.5, and 10.1 before 10.1-118.7 allows users to "breakout" of the shell via unknown vectors.
Security (NVD + CISA KEV)
CVE-2014-2321· CVSS 10.0 HIGH
NVD
CVE-2014-2321· CVSS 10.0 HIGH
NVD · 2014-03-11
web_shell_cmd.gch on ZTE F460 and F660 cable modems allows remote attackers to obtain administrative access via sendcmd requests, as demonstrated by using "set TelnetCfg" commands to enable a TELNET service with specified credentials.
Security (NVD + CISA KEV)
CVE-2014-0505· CVSS 10.0 HIGH
NVD
CVE-2014-0505· CVSS 10.0 HIGH
NVD · 2014-03-14
Adobe Shockwave Player before 12.1.0.150 allows remote attackers to execute arbitrary code or cause a denial of service (memory corruption) via unspecified vectors.
Security (NVD + CISA KEV)
CVE-2014-1704· CVSS 10.0 HIGH
NVD
CVE-2014-1704· CVSS 10.0 HIGH
NVD · 2014-03-16
Multiple unspecified vulnerabilities in Google V8 before 3.23.17.18, as used in Google Chrome before 33.0.1750.149, allow attackers to cause a denial of service or possibly have other impact via unknown vectors.
Security (NVD + CISA KEV)
CVE-2014-1708· CVSS 10.0 HIGH
NVD
CVE-2014-1708· CVSS 10.0 HIGH
NVD · 2014-03-16
The boot implementation in Google Chrome OS before 33.0.1750.152 does not properly consider file persistence, which allows remote attackers to execute arbitrary code via unspecified vectors.
Security (NVD + CISA KEV)
CVE-2014-1512· CVSS 10.0 HIGH
NVD
CVE-2014-1512· CVSS 10.0 HIGH
NVD · 2014-03-19
Use-after-free vulnerability in the TypeObject class in the JavaScript engine in Mozilla Firefox before 28.0, Firefox ESR 24.x before 24.4, Thunderbird before 24.4, and SeaMonkey before 2.25 allows remote attackers to execute arbitrary code by triggering extensive memory consumption while garbage collection is occurring, as demonstrated by improper handling of BumpChunk objects.
Security (NVD + CISA KEV)
CVE-2014-2523· CVSS 10.0 HIGH
NVD
CVE-2014-2523· CVSS 10.0 HIGH
NVD · 2014-03-24
net/netfilter/nf_conntrack_proto_dccp.c in the Linux kernel through 3.13.6 uses a DCCP header pointer incorrectly, which allows remote attackers to cause a denial of service (system crash) or possibly execute arbitrary code via a DCCP packet that triggers a call to the (1) dccp_new, (2) dccp_packet, or (3) dccp_error function.
Security (NVD + CISA KEV)
CVE-2012-4886· CVSS 10.0 HIGH
NVD
CVE-2012-4886· CVSS 10.0 HIGH
NVD · 2014-03-24
Stack-based buffer overflow in wpsio.dll in Kingsoft WPS Office 2012 possibly 8.1.0.3238 allows remote attackers to execute arbitrary code via a long BSTR string.
Security (NVD + CISA KEV)
CVE-2014-1300· CVSS 10.0 HIGH
NVD
CVE-2014-1300· CVSS 10.0 HIGH
NVD · 2014-03-26
Unspecified vulnerability in Apple Safari 7.0.2 on OS X allows remote attackers to execute arbitrary code with root privileges via unknown vectors, as demonstrated by Google during a Pwn4Fun competition at CanSecWest 2014.
Security (NVD + CISA KEV)
CVE-2014-1303· CVSS 10.0 HIGH
NVD
CVE-2014-1303· CVSS 10.0 HIGH
NVD · 2014-03-26
Heap-based buffer overflow in Apple Safari 7.0.2 allows remote attackers to execute arbitrary code and bypass a sandbox protection mechanism via unspecified vectors, as demonstrated by Liang Chen during a Pwn2Own competition at CanSecWest 2014.
Security (NVD + CISA KEV)
CVE-2014-0506· CVSS 10.0 HIGH
NVD
CVE-2014-0506· CVSS 10.0 HIGH
NVD · 2014-03-27
Use-after-free vulnerability in Adobe Flash Player before 11.7.700.275 and 11.8.x through 13.0.x before 13.0.0.182 on Windows and OS X and before 11.2.202.350 on Linux, Adobe AIR before 13.0.0.83 on Android, Adobe AIR SDK before 13.0.0.83, and Adobe AIR SDK & Compiler before 13.0.0.83 allows remote attackers to execute arbitrary code, and possibly bypass an Internet Explorer sandbox protection mechanism, via unspecified vectors, as demonstrated by VUPEN during a Pwn2Own competition at CanSecWest 2014.
Projects + Resources (Discovery)
10 item(s)
Projects + Resources (Discovery)
GitHub - YosysHQ/nextpnr: nextpnr portable FPGA place
Brave Search
GitHub - YosysHQ/nextpnr: nextpnr portable FPGA place and route tool · GitHub new
Brave Search
For Cyclone V support, clone Mistral to $HOME/mistral or another location and pass this path as -DMISTRAL_ROOT=$HOME/mistral to CMake. Then build and install nextpnr-mistral using the following commands:
Projects + Resources (Discovery)
Yosys+nextpnr: an Open Source Framework from Verilog
Brave Search
Yosys+nextpnr: an Open Source Framework from Verilog ... new
Brave Search
// Apply these mapping rules to Yosys’ generic LUT cells ... IV. NEXTPNR – PACK, PLACE, ROUTE & BITSTREAM-GEN. nextpnr is an open-source, timing-driven, place-and-route · framework targeting real-world FPGA silicon supporting Linux,

Projects + Resources (Discovery)
Yosys+nextpnr: An Open Source Framework from Verilog
Brave Search
Yosys+nextpnr: An Open Source Framework from Verilog to Bitstream for Commercial FPGAs | IEEE Conference Publication | IEEE Xplore new
Brave Search
<strong>This paper introduces a fully free and open source software (FOSS) architecture-neutral FPGA framework comprising of Yosys for Verilog synthesis, and nextpnr for placement, routing, and bitstream generation</strong>.
Projects + Resources (Discovery)
GitHub - google/skywater-pdk: Open source process design
Brave Search
GitHub - google/skywater-pdk: Open source process design kit for usage with SkyWater Technology Foundry's 130nm node. · GitHub new
Brave Search
Open source process design kit for usage with SkyWater Technology Foundry's 130nm node. - google/skywater-pdk
Projects + Resources (Discovery)
SkyWater Announces Availability of Cadence Open-Source PDK
Brave Search
SkyWater Announces Availability of Cadence Open-Source PDK and Reference Design for SkyWater’s 130 nm Process - Skywater Technology new
Brave Search
The Cadence VLSI Fundamentals Education Kit is a CMOS VLSI Design course structured to enhance academic curriculum, which contains several lecture presentations to teach the fundamental theoretical knowledge of VLSI design. It also contains four labs that explain the design of a mixed-signal IC using Cadence’s latest tools: Virtuoso Studio, Genus Synthesis Solution, Innovus Implementation System, Xcelium Logic Simulator, Pegasus Verification System, and Spectre Simulation Platform. The design is based on a simple Arm-based microprocessor and is being migrated to the SKY130 PDK. ... SkyWater (NASDAQ: SKYT) is a U.S.-based semiconductor manufacturer and a DMEA-accredited Category 1A Trusted Foundry.
Projects + Resources (Discovery)
Sky130 PDK | UCSC VLSI-DA Chip Tutorials
Brave Search
Sky130 PDK | UCSC VLSI-DA Chip Tutorials new
Brave Search
Tim Ansell — SkyWater PDK: Fully open source manufacturable PDK for a 130 nm process
Projects + Resources (Discovery)
An Open-Source Toolkit To Expand Bioinformatics Training
Brave Search
An Open-Source Toolkit To Expand Bioinformatics Training in Infectious Diseases - PMC new
Brave Search
In 2015, we began a semester-long course with the goal of empowering students to take a “do-it-yourself” (DIY) approach to learning transcriptomics using the R programming environment and the Bioconductor suite of software packages. Over the past 6 years, we have refined this course to create a comprehensive, fully virtual, and open-source set of resources suitable for learners ranging from high school students to graduate students and postgraduate professionals.
Projects + Resources (Discovery)
Home - Bioinformatics.org
Brave Search
Home - Bioinformatics.org new
Brave Search
There are two key repositories: <strong>https://github.com/google-deepmind/alphagenome</strong> – This provides the Python SDK and programmatic access to the hosted API. <strong>https://github.com/google-deepmind/alphagenome</strong>_research – This contains the model source code, weights, variant scoring tools, and related ...

Projects + Resources (Discovery)
Open Neuromorphic is a global community fostering
Brave Search
Open Neuromorphic is a global community fostering education, research, and open-source collaboration in brain-inspired AI and hardware. new
Brave Search
Submit your open-source neuromorphic projects for transparent community review and recognition through the ONR Program.
Projects + Resources (Discovery)
1 Simphony: An open-source photonic integrated circuit
Brave Search
1 Simphony: An open-source photonic integrated circuit simulation framework new
Brave Search
Abstract—We present Simphony, a free and open-source soft- ware toolbox for abstracting and simulating photonic integrated